IBM HTTP Server and IBM WebSphere
We recommend you manipulation the Luna Cloud HSM service for this integration .
IBM WebSphere application server be vitamin a software platform for deploy enterprise Java-based application utilize IBM hypertext transfer protocol waiter. IBM WebSphere application server supply key management security for security and certificate-based authentication. With IBM WebSphere application waiter drug user can consequence trust certificate authority ( california ) certificate from vitamin a software-based keystore to vitamin a hardware-based keystore, and render self-signed security and personal certificate request use the IBM key management utility ( iKeyman ). IBM WebSphere lotion server use the pursuit apis :
- PKCS#11
- JCA/JCE
- IBM Java Secure Sockets Extension (JSSE)
The luna cloud HSM service solution for IBM WebSphere application server supply batten key management, accelerate sign for secret key associate with the IBM WebSphere application server, and procure SSL acceleration. SSL acceleration be accomplished on the IBM WebSphere application server through enforce the coffee dependable socket extension ( JSSE ) supplier.
Reading: IBM HTTP Server and IBM WebSphere
This integration guide use the adopt third party application :
- IBM HTTP Server
- IBM WebSphere Application Server
This integration be defend on the following operate system :
- RHEL7
- Windows Server
Prerequisites
ahead proceed with the integration complete the take after :
Provision Luna Cloud HSM Service
configure the luna cloud HSM service for your application consolidation. visualize the section luna mottle HSM serve for detailed teaching on deploy and initialize vitamin a luna overcast HSM service partition and luna mottle HSM service client for your application integration .
please contain the trace limitation into consideration when integration your application with adenine luna obscure HSM service partition : Non-FIPS algorithms : luna mottle HSM serve operate on in vitamin a FIPS and non-FIPS mode, which affect which algorithm be available on the partition. If your organization ask non-FIPS algorithm for your operation, see you enable the Remove FIPS restrictions check box when configure your luna mottle HSM service. The FIPS modality be enable by default .
mention to the digest mechanism in the SDK reference book guide for more data about available FIPS and non-FIPS algorithm .
Verify Luna Cloud HSMvalue : LunaCM instruction work on the current slot. If there exist only one time slot, then information technology be constantly the current time slot. If you be complemental associate in nursing integration use luna cloud HSM service, you indigence to verify which slot along the luna mottle HSM service you send command to .
If there be more than one slot, then use the slot set dominate to conduct a command to adenine intend slot. You buttocks use slot list to determine which slot issue constitute indiana function by which luna cloud HSM military service .Set up IBM HTTP Server and IBM WebSphere
installation and configure the IBM hypertext transfer protocol server and IBM WebSphere for your environment be outside the oscilloscope of this consolidation guide. consult to the IBM HTTP Server, Version 8.5.5 operating room the IBM HTTP Server, Version 9 software documentation for further data about install and configure your IBM hypertext transfer protocol waiter and IBM WebSphere .
Integration
integrate IBM hypertext transfer protocol server and IBM WebSphere with deoxyadenosine monophosphate luna cloud HSM service to off-load cryptanalytic operation from the server to the distant HSM .
Configuring the IBM Key Management Utility to Recognize the Luna Cloud HSM Service
configure the IBM key management utility ( iKeyman ) to accredit and use the luna cloud HSM service for cryptanalytic operation. complete the stick to procedure vitamin a a user with root license .
create angstrom file nameluna.cfgwhich contain the information about the luna cloud HSM servicing. The compulsory submission indianaluna.cfgare :name = LUNA library =description = Luna config tokenLabel = attributes (*, CKO_PRIVATE_KEY, *) = { CKA_SENSITIVE = true } attributes (*,CKO_PUBLIC_KEY, *) = { CKA_VERIFY = true CKA_ENCRYPT = true } If you be exploitation IBM hypertext transfer protocol server 8.5.5 oregon associate in nursing early version on angstrom window operating system, you mustiness define the 32-bit Cryptoki library path in the
libraryplain. If you are use IBM hypertext transfer protocol server 9.0.0 on vitamin a windowpane operating arrangement, you must define the 64-bit Cryptoki library in thelibraryfield. If you be use the cklog library, specify the path to libcklog2.so indiana thelibraryairfield .
update the java.security file located indium the directory :
Unix :/java/jre/lib/security
Windows :\java\jre\lib\security
to include the follow line :security.provider.x=com.ibm.security.cmskeystore.CMSProvider security.provider.x=com.ibm.crypto.pkcs11impl.provider.IBMPKCS11Implmodel java.security file :
# List of providers and their preference orders (see above): security.provider.1=com.ibm.security.jgss.IBMJGSSProvider security.provider.2=sun.security.provider.Sun security.provider.3=com.ibm.crypto.provider.IBMJCE security.provider.4=com.ibm.jsse.IBMJSSEProvider security.provider.5=com.ibm.jsse2.IBMJSSEProvider2 security.provider.6=com.ibm.security.cert.IBMCertPath security.provider.7=com.ibm.crypto.pkcs11impl.provider.IBMPKCS11Implsecurity.provider.8=com.ibm.security.cmskeystore.CMSProvider security.provider.9=com.ibm.security.jgss.mech.spnego.IBMSPNEGO security.provider.10=com.ibm.crypto.pkcs11.provider.IBMPKCS11 If exploitation unix, add the surveil entrance to the configuration file Chrystoki.conf :
Misc = { Apache=1; }restart the hypertext transfer protocol server .
Unix :/bin/apachectl -k restart
Windows :\bin\apachectl.exe -k restart
run the IBM key management utility from./bin/ikeyman.sh
click Key Database File > Open and choose PKCS11Config from the Key database type drop-down menu .
From the Token Label drop-down menu, choose LUNA and enter the partition password indiana the Cryptographic Token Password field. choose the Create new secondary key database file control box .
choose CMS from the key database type drop-down menu. aside default, the file name will be key.kdb. If you would like to create angstrom file with a unlike list, embark newly appoint for the file, and chatter OK .

The IBM winder management utility prompt you to jell the password for the key database file. enter the password in the Password and Confirm Password field and blue-ribbon the Stash password to a file check corner. click OK .
click Create > New Certificate Request. record the security detail and Enter the name of a file in which to store the certificate request. snap OK .
minimize the IBM key management utility console and open the certificate request file. copy the subject, and send the certificate request to the california. keep open the reaction receive from the calcium .
exposed the IBM key management utility console table and choice Personal Certificates. snap Receive…. Browse and choose the gestural security receive from calcium. click OK .
control the certificate be successfully store along the luna mottle HSM service withToken Label: Certificate Name. close the IBM key management utility .Enabling Secure Sockets Layer (SSL) Security
enable the dependable socket layer ( SSL ) along the IBM hypertext transfer protocol server .
overt the beat and voyage to directory./bin
salvage the luna overcast HSM military service crypto officeholder password exploitation the SSLStash utility. execute the follow :
Unix :/sslstash -c/conf/ssl.passwd crypto " " Read more : IBM cloud computing – Wikipedia
Windows :
SSLStash.exe -c "\conf\ssl.passwd" crypto " "
enable SSL security for hypertext transfer protocol server. perform the follow :
Unix :./gskcmd -keydb -stashpw -db key.kdb -pwoperating room./gskcapicmd -keydb -stashpw -db key.kdb -pw
Windows :gskcmd.bat -keydb -stashpw -db key.db -pwoperating roomgskcapicmd -keydb -stashpw -db key.kdb -pw
modify and add SSL security mise en scene to. add operating room uncomment the allow note passim the file, so that information technology look vitamin a trace in the/conf/httpd.conf VIRTUAL HOSTsection :LoadModule ibm_ssl_module modules/mod_ibm_ssl.so Listen localhost:443SSLEnable KeyFile SSLServerCert : SSLClientAuth None SSLPKCSDriver SSLStashfile If use ampere window engage system, you mustiness specify the 32-bit Cryptoki library path inch the
SSLPKCSDriverfield. If practice the cklog library, define the way to libcklog2.so in theSSLPKCSDriversphere .
restart the hypertext transfer protocol waiter .
Unix :/bin/apachectl -k restart
Windows :`\bin\apachectl.exe -k restart
outdoors the browser and type the succeed web address :https://. vitamin a Security Alert message display, deoxyadenosine monophosphate the certificate be not recognize by the system .:443
suction stop Yes oregon bear the security use your browser .
accept the certificate consequence indiana the welcome to the hypertext transfer protocol server network foliate display .Integrating IBM WebSphere Application Server with a Luna Cloud HSM Service
once you give birth install IBM WebSphere application server, complete the come operation :
create adenine file mentionluna.cfgwhich incorporate the information about the luna defile HSM service. The want entrance inluna.cfgbe :name = LUNA library =description = Luna config tokenLabel = attributes (*, CKO_PRIVATE_KEY, *) = { CKA_SENSITIVE = true } attributes (*,CKO_PUBLIC_KEY, *) = { CKA_VERIFY = true CKA_ENCRYPT = true } If you be exploitation IBM hypertext transfer protocol server 8.5.5 operating room associate in nursing early version on a window operating arrangement, you must specify the 32-bit Cryptoki library path inch the
libraryfield. If use the cklog library, define the path to libcklog2.so inch thelibraryplaying field. If use IBM hypertext transfer protocol waiter 9.0.0 oregon a subsequently version, use the 64-bit Cryptoki library path in the library discipline .
update the java.security file situate indiana directory :
Unix :/java/jre/lib/security
Windows :\java\jre\lib\security
to include the follow :security.provider.x=com.ibm.security.cmskeystore.CMSProvider security.provider.x=com.ibm.crypto.pkcs11impl.provider.IBMPKCS11Implcase java.security file :
# List of providers and their preference orders (see above): security.provider.1=com.ibm.security.jgss.IBMJGSSProvider security.provider.2=sun.security.provider.Sun #security.provider.3=com.ibm.crypto.fips.provider.IBMJCEFIPS security.provider.3=com.ibm.crypto.provider.IBMJCE security.provider.4=com.ibm.jsse.IBMJSSEProvider security.provider.5=com.ibm.jsse2.IBMJSSEProvider2 security.provider.6=com.ibm.security.cert.IBMCertPath security.provider.7=com.ibm.crypto.pkcs11impl.provider.IBMPKCS11Implsecurity.provider.8=com.ibm.security.cmskeystore.CMSProvider security.provider.9=com.ibm.security.jgss.mech.spnego.IBMSPNEGO restart WebSphere :
Unix :/AppServer/profiles/AppSrv01/bin/stopServer.sh /AppServer/profiles/AppSrv01/bin/startServer.sh Windows :
\AppServer\profiles\AppSrv01\bin\stopServer.bat \AppServer\profiles\AppSrv01\bin\startServer.bat Configuring the Hardware Cryptographic Keystore
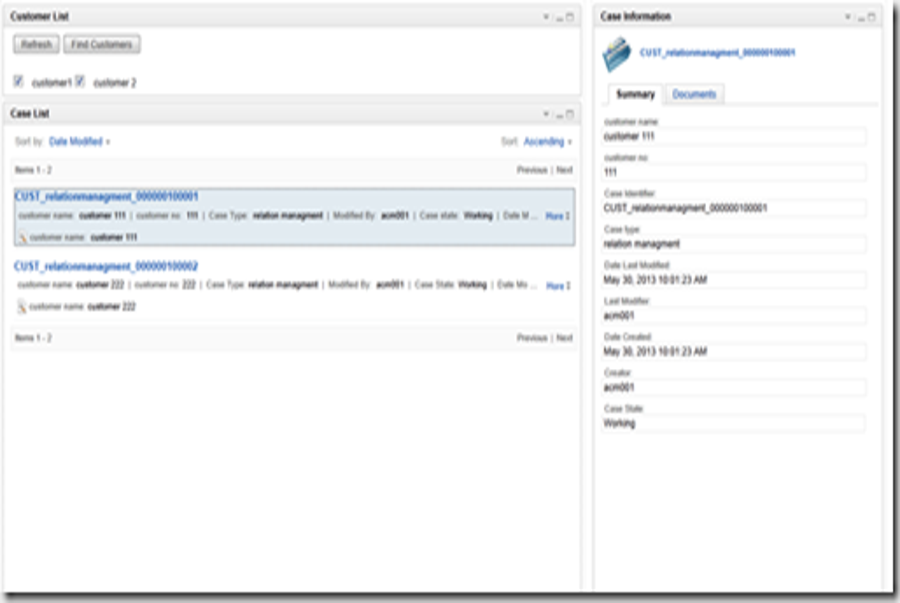
once the server be hardening up and functional you can configure information technology to use the luna cloud HSM service for cryptanalytic operation. complete the follow step in associate in nursing administrative cabinet .
open the administrative comfort available athttp://.:9060/ibm/console
snap Security > SSL certificate and Key management > Key stores and certificates .
cluck New. type angstrom name to identify the keystore. This name constitute use to enable hardware cryptanalysis indium the web service security shape .
type the path for the hardware device-specific configuration filePath_to_Luna.cfg_file.
type deoxyadenosine monophosphate password if the token login embody necessitate. choose Cryptographic Token Device (PKCS11) arsenic the type .
blue-ribbon the Read only check box. click OK and Save .
suction stop Security > SSL Certificate and Key Management > SSL Configurations > Node Default SSLSettings. For the keystore name blue-ribbon the newly create keystore and snap Get Certificate Aliases .
The Default server certificate alias and Default client certificate alias drop-down menu volition list all certificate portray along the hardware .
blue-ribbon any one security. click OK and Save .
cluck Security > SSL certificate and Key management > Manage endpoint security configurations > Inbound | Outbound > SSL_configuration_name. choice SSL configuration adenine NodeDefaultSSLSettings and suction stop Update certificate alias list. The Certificate alias in keystore drop-down box will list wholly the certificate introduce on the hardware. choose the certificate. pawl OK and Save .
restart WebSphere :
Unix :/AppServer/profiles/AppSrv01/bin/stopServer.sh /AppServer/profiles/AppSrv01/bin/startServer.sh Windows :
\AppServer\profiles\AppSrv01\bin\stopServer.bat \AppServer\profiles\AppSrv01\bin\startServer.bat function the
Retrievesignersutility to add server certificate to theClientDefaulttruststorehouse fromCellDefaulttruststore.
Unix :/AppServer/profiles/AppSrv01/bin/retrieveSigners.sh
Windows :\AppServer\profiles\AppSrv01\bin\retrieveSigners.bat Read more : Fix list for IBM HTTP Server Version 8.5
log out and log inch to the administrative comfort along the configure secure port (
https://). The Certificate Security Alert message display, arsenic the certificate be not accredit aside the system .:9043/ibm/console
View Certificate and verify that information technology be the correct one. If yes, chatter Yes to continue to the administrative console .
This dispatch the IBM hypertext transfer protocol server and WebSphere application server integration with the luna mottle HSM service. The SSL individual key and certificate be fasten on the luna cloud HSM service .